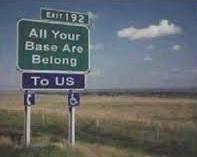
By now you’ve heard that we had another mass shooting in the United States. It was our 351st of the year — fourteen more and we get a free ice cream! The shooting was in San Bernardino and #SanBernadino was trending on Twitter. The world already thinks we’re violent, guys. Do we need them to think we’re stupid, too? Learn to spell the town that’s currently under fire.
By now you’ve heard that we had another mass shooting in the United States. It was our 351st of the year — fourteen more and we get a free ice cream! The shooting was in San Bernardino and #SanBernadino was trending on Twitter. The world already thinks we’re violent, guys. Do we need them to think we’re stupid, too? Learn to spell the town that’s currently under fire.
Wars and shootings are how America learns geography. Nobody knew where Baghdad was until we bombed it.
So this particular shooter left an office holiday party in a fit of rage. He returned with his wife and they shot up the place. So this much is clear: Office parties suck! Let’s face it. The only thing we have in common is we applied for a job in the same company. Now we have assholes showing up with guns. Your JoeDog would rather stay at home and hack some code.
We learned this particular office asshole was stockpiling ammunition and bombs. When police searched his vehicle, they found 6000 rounds of ammunition and a dozen pipe bombs. Now that’s a guy who hates his co-workers.
Some of you may think Your JoeDog’s a bit flippant about this whole ordeal, telling jokes and dropping snark. For the past thirty years we’ve tried “thoughts and prayers.” When someone shot up a public place, we gave thoughts and prayers. Over the last thirty years we gave a lot of thoughts and a lot of goddamn prayers.
Well guess what? They don’t fscking work. Your JoeDog’s just going to do what he does best: Toss spit balls from the back of the room. You know what’s annoying and gross? Spitballs. If we plaster the people who own this country with enough of them maybe they’ll finally act. God knows thoughts and prayers don’t work.